
The Importance of Fire Watch Guards
Fires can be devastating and deadly, destroying properties and lives in mere minutes. With increasing occurrences of fires in both

Fires can be devastating and deadly, destroying properties and lives in mere minutes. With increasing occurrences of fires in both

As a resident of Perth, you know that home security is of utmost importance. That’s why you need to consider

The role of Qualities of a Good Pandemic Response Security Guards is drastically changing from security role as they have

Keeping your family and home safe and secure is a top priority. One way to achieve this is by installing

Spy cam equipment are not just for high-level military stuff. Forget what you’ve read in the espionage novels. These days,

What are DSC alarms? DSC alarms are a type of home security system that is becoming increasingly popular in Perth.

In Perth, access control systems are used to restrict access to certain areas. These systems can be used in a

Many company’s make use of Asset Protection Security not only to protect their cash in transit or goods in transit
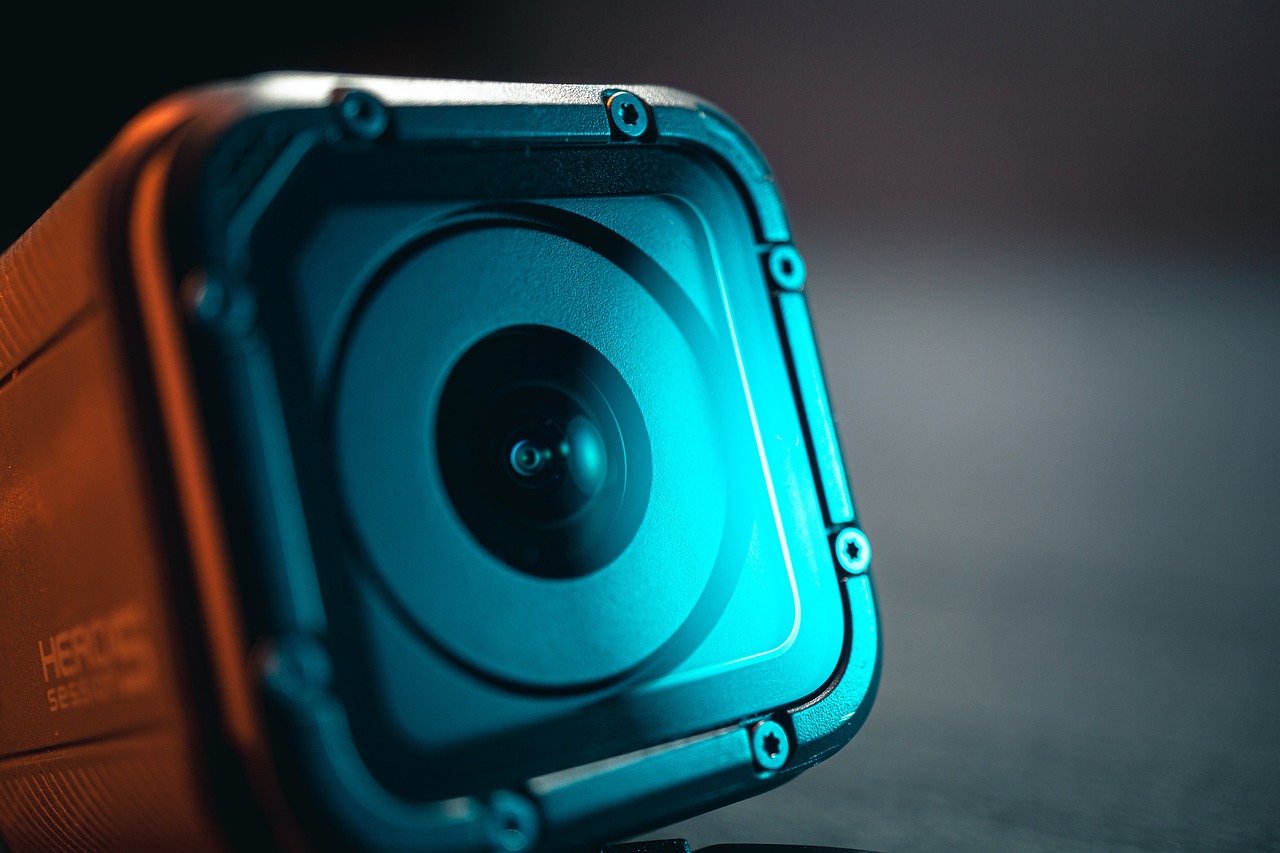
It is fascinating how tiny cameras can be placed almost anywhere. With Spy Cam Equipment, you can keep an eye

What are DSC alarms? DSC alarms are a type of home security system that is becoming increasingly popular in Perth.
Copyright © 2025 | Powered by Word-Weight
Copyright © 2025 | Powered by Word-Weight